# Description
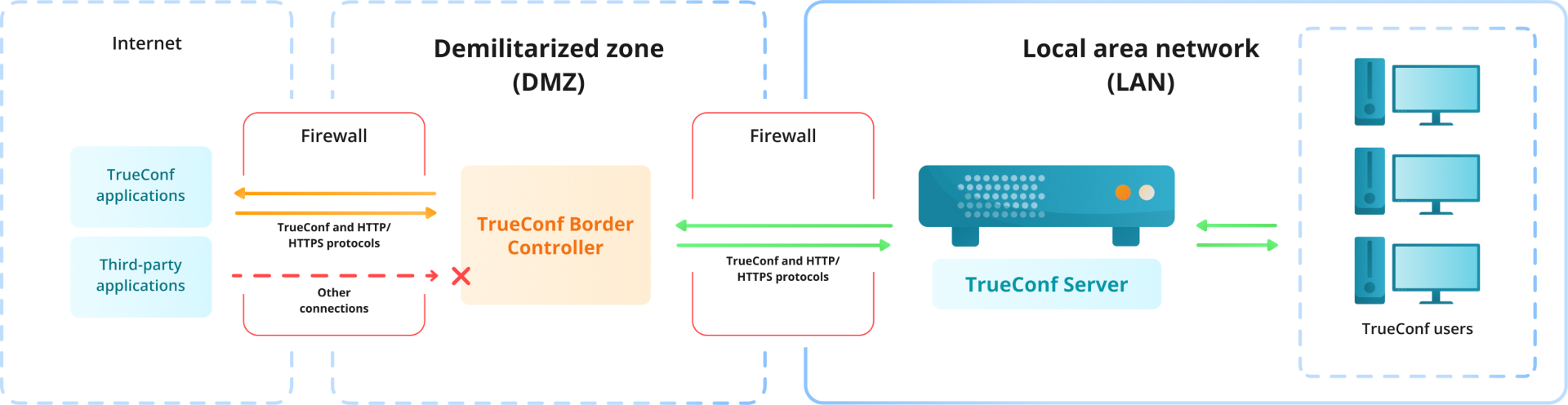
The all-in-one TrueConf Enterprise solution includes the TrueConf Border Controller extension that provides external users (outside the corporate network environment) with secure access to video conferencing servers.
TrueConf Border Controller is a separate extension that acts as a border controller designed to be installed in the DMZ (demilitarized zone) of the corporate network and allowing only secure traffic from TrueConf client applications.
# Parts of the solution
The extension consists of two components that validate traffic via TrueConf and HTTP/HTTPS protocols respectively.
We recommend using HTTPS on TrueConf Server since it improves the security of the web server resources and ensures the work of the scheduler, real-time meeting management tool, browser-based conference participation and access to a user’s personal area.
Components of TrueConf Border Controller have to be configured separately, and are able to work independently of each other which means that it is possible to configure traffic transfer only via TrueConf protocol, but not via HTTPS.
How TrueConf Border Controller works:
# How the solution works
The TrueConf Border Controller extension is installed in the DMZ.
The extension checks the protocols of the traffic that comes from the external network.
If the traffic does not come via TrueConf or HTTPS protocol, it will simply be rejected.
If the extension detects traffic from TrueConf client applications or via HTTPS, the connection will be accepted and a new connection will be created from TrueConf Border Controller to the selected TrueConf Server or TrueConf Enterprise instance. When the connection is established, the packets from the application will be sent via the new connection to the video conferencing server (only TrueConf and HTTPS traffic is allowed). This does not only ensure the transfer of media streams, but also ensures the work of the scheduler, access to the video conferencing server web pages, federation and other features.
If necessary, the traffic from TrueConf Border Controller to the video conferencing server can be encrypted with the help of multiple symmetric algorithms, including PSK (Pre-Shared Key) (opens new window).
Apart from encryption, the extension does not perform any additional operations on traffic like analysis, saving, transfer to third-party services, and so forth.
So, the protection of a video conferencing server installed inside the corporate network is based on the following principles:
TrueConf Border Controller does not create a new connection to TrueConf Server until it determines that the packets are coming from TrueConf client application or via the secure HTTPS protocol.
No external traffic is directed to the video conferencing server by TrueConf Border Controller. This includes the traffic via SIP/H.323/RTP and others. For example, only TrueConf client applications will be able to connect to TrueConf Server from outside the network.
The IP address of the video conferencing server inside the corporate network is hidden. The server only has to be connected to the DMZ, but it does not have to be connected to the Internet. Please note that server federation will be impossible if there is no connection with the Internet.
Additionally, it is possible to encrypt the traffic sent via TrueConf protocol.
Every component of the extension is an executable file that does not require installation. It can be run from the console or added as a service on Windows or daemon on Linux.